The U.S. accused seven Iranians Thursday of carrying out a massive computer hacking scheme on behalf of the Iranian government to disrupt the Internet operations at 46 American financial institutions.
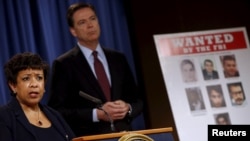
U.S. Attorney General Loretta Lynch said the hackers at two Iran-based computer companies worked for Tehran, including the Revolutionary Guard Corps. She said the seven experienced hackers coordinated a cyberattack campaign from late 2011 to mid-2013 on the banks, including some of the largest in the U.S. based in New York, that flooded their web sites with Internet traffic, crashed their servers and blocked customers from accessing their accounts.
Lynch, the country's top law enforcement official, said the cyber intrusions cost the banks, such as JP Morgan Chase and Bank of America, "tens of millions of dollars" to repair their company websites.
In addition, the U.S. alleged that one of the Iranians hacked into the control system of a small irrigation dam outside New York and would have been able to control its water levels and flow rates, but for the fact that the dam was undergoing maintenance work at the time of the computer intrusion and had been shut down.
Lynch described the computer attacks on the financial institutions as "relentless, systematic and widespread."
"This case is a reminder," she said, "of the seriousness of cyber threats to our national security. And we believe that they were conducted with the sole purpose of undermining the targeted companies and damaging the online operation of America's free market."
Despite Lynch's high-profile announcement of the case in Washington, it is unclear when or if any actual prosecution of the case against the seven Iranians might occur since they have not been apprehended and there is no indication that Tehran would turn them over to U.S. authorities. The U.S. has no extradition treaty with Iran.
But Lynch said, "Fugitives don't remain that way forever."
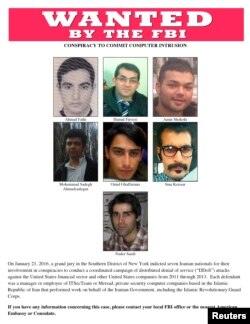
The seven accused computer workers were employed by ITSec Team and Mersad Company, the U.S. alleged, and carried out their hacking for 176 days. They were identified as Ahmed Fathi, 37 years old; Hamid Firoozi, 34; Amin Shokohi, 25; Sadegh Ahmadzadegan, also known as Nitr0jen26, 23; Omid Ghaffarinia, also known as PLuS, 25; Sina Keissar, 25, and Nader Saedi, also known as Turk Server, 26.
The charges add to the contentious and complicated relations between Washington and Tehran.
The U.S. and five other world powers implemented a nuclear agreement with Iran in January that blocks Tehran from manufacturing nuclear weaponry in exchange for ending sanctions that hobbled its economy.
But in addition to the cybersecurity charges Thursday, the U.S. added two Iranian units involved in its ballistic missile program to its sanction blacklist, two weeks after Iran conducted missile tests that Washington called "provocative and destabilizing."
The action freezes any of the assets under U.S. jurisdiction held by Shadid Nuri Industries and Shadid Movahed Industries, both units of the Shadid Hemmat Industrial Group that is responsible for Iran's ballistic missile program.
On Wednesday, U.S. authorities unsealed an indictment accusing a consultant to Iran's United Nations mission, Ahmed Sheikhzadeh, of violating U.S. trade sanctions against Tehran.
Similar sanction-related charges against others were dropped in January as the nuclear pact was implemented and Iran freed Americans it had detained.